Effortless digital experiences for customer service
Build easy-to-use digital experiences that automate customer service through seamless self-serve and agent-led interactions.



Easily offer digital options for any customer need
Proven with millions of customers every month
- 40k
Agents delivering digital customer service daily
- 10M+
Pages of paper saved with digital contracts and agreements

- 50%+
Inbound calls diverted to digital self-service automaton

Build advanced digital customer services in a fraction of the time
Automate any step in the customer journey
Digital Self-Service
Offer digital tools in any channel to deflect calls and automate manual processes.
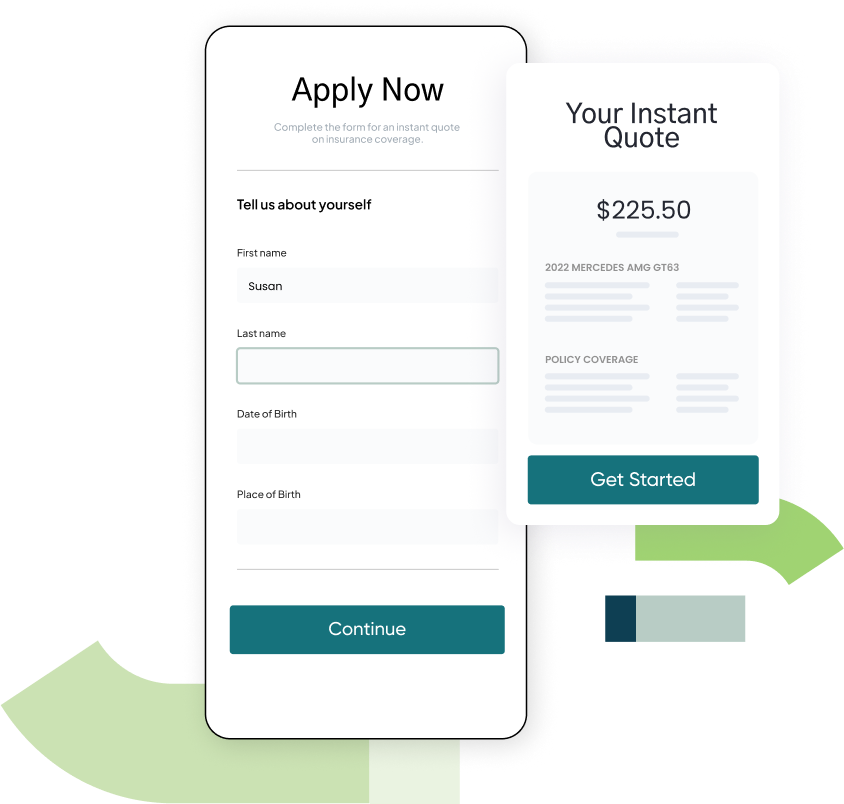
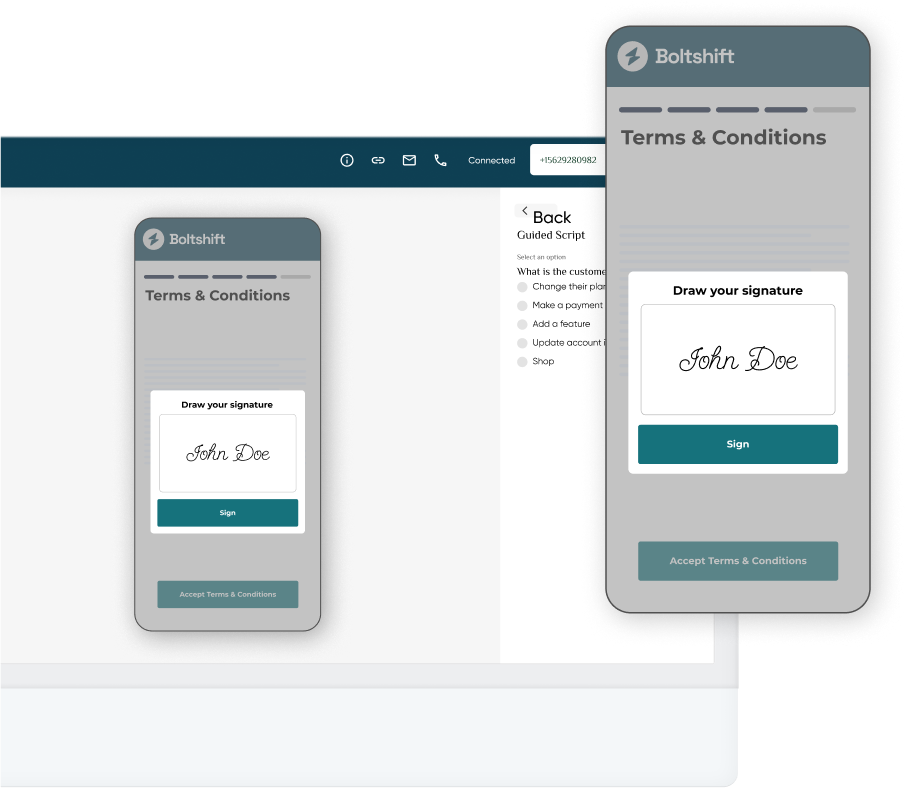
Agent-Led Collaboration
Deliver digital tools with a text link. Share customer screens and shorten support calls.
Proactive Care
Anticipate needs based on customer data and offer solutions to prevent problems.

Customer-obsessed leaders love Callvu
"Callvu allows us to quickly address customer pain points with easy-to-use digital self-service options that cut support costs and increase customer satisfaction."

David Williams
Vice President, Automation, AT&T"Callvu powers our Visual Call Center, giving customers the option to self-serve via SMS. 400,000 customers now choose self-service monthly, and the figure continues to climb."

Anca Radu
Product Manager, eCommerce, BT"Callvu has enabled MOST Technologies and our clients to shorten development time by 90% for digital collaboration experiences between customers and agents."

Omry Genossar
Vice President, Products, MOST Technologies






Want to see more? No problem.
Get in touch with our team or create a free account with just your email.
Digital Experience Platform FAQs
What is a customer experience platform and why does it matter?
A customer experience platform (CEP) helps analyze and pinpoint relevant customer behaviors and preferences and enables brands to deliver experiences that increase customer satisfaction.
A great customer experience platform helps you orchestrate ideal customer experiences in whatever form each user prefers.
What are the most important elements of a strong customer experience platform solution?
All customer experience platforms are not the same. When choosing the right solution for your business, there are many factors to consider. Here are some of the most important elements to look for.
- Post-Sales Experience Focus: The customer journey is just beginning when a prospect makes their first purchase. A great customer experience platform enables you to create great customer-facing experiences that help customers get the benefits, service, and support they need. Since front-end experiences are the primary means customers form opinions and derive customer satisfaction from a brand, customer-facing digital experiences are the most valuable and essential outputs of a customer experience platform. While ensuring an inviting sales experience is also very important, pleasing existing customers should be the top priority.
- Self-Service or Agent-Assisted Use Cases: Your CEP should make it easy to create digital experiences in both self-service and agent-assisted customer interaction scenarios. By making simple apps that can be used in these two critical ways, you drive maximum digital adoption, reduce contact center costs, and please more customers.
- Multichannel Support: Look for a platform that creates experiences that can be delivered in multiple support channels, including web, mobile, visual IVR, on-premise, and other digital touchpoints. This will enable you to provide a seamless and consistent experience across all channels.
- Integration: Look for a digital customer experience platform that can integrate with the existing systems and applications within your organization, such as ERP, CRM, account management, customer data platform, call center, IVR, and e-commerce platforms. This will enable you to streamline workflows and improve operational efficiency.
- Ease of Use: The platform should be user-friendly and easy to use, with a simple, intuitive interface. This will enable your team to learn and use the platform quickly and effectively. Usability is critical when you are trying to create many experiences to address issues customers face every day.
- Scalability: Look for a platform that can scale with your business as it grows, with the ability to handle increasing volumes of customer data and interactions.
By factoring these considerations into your decision, you can make a better choice – ensuring the software meets all your needs.
Why is it critical to leverage customer experience platforms for both sales and post-sales customer experiences?
Many companies have spent heavily streamlining and automating sales experiences to maximize new customer acquisition. Of course, that has tremendous value. Every business wants to maximize the size and growth rate of its customer base.
Equally important is empowering better post-sales customer experiences. These experiences ensure the long-term health and vitality of your business or organization.
Both positive sales and post-sales experiences can increase customer loyalty and retention. Customers who have a good experience after purchasing a product or service are more likely to become repeat customers, which can lead to increased revenue and profitability for the business. Data show that it is much less expensive to drive an incremental purchase from an existing customer than to convert a new one. Most companies depend on ongoing business relationships with their customers.
Customers with positive sales and post-sales experiences are more likely to refer friends and family to the business. This can help generate new business, reduce customer acquisition costs, and cost-effectively increase brand awareness. Additionally, having all friends or family members use a single solution provider in some industries helps minimize churn. In today’s socially connected world, word-of-mouth recommendations are an important source of new business.
Providing positive post-sales experiences can also lead to opportunities for upselling and cross-selling. Customers with positive experiences are more likely to trust the business and consider purchasing additional products or services. Sales experiences help ensure an engagement starts strong. Post-sales engagements keep the relationship strong and escalate retention and loyalty.
How does a customer experience platform enhance customer service and customer service ratings (CSAT)?
Customer experience platforms can enhance the customer service experience in several ways:
Make Customer Support Omnichannel: A customer experience platform enables businesses to offer support across multiple channels, such as phone, email, chat, social media, and messaging. This lets customers choose their preferred channel and get help quickly and efficiently.
Deliver Personalized Experiences: By collecting, updating, and delivering customer data through its API gateway, a CEP can personalize customer interactions. For example, it can recommend products or services based on the customer's browsing or purchase history or address the customer by name.
Empowering More Self-Service: Often, customer experience platforms are implemented largely to enable self-service and maximize digital adoption. Additionally, customer experience platforms are often used to allow customers to find answers to their questions through self-service options such as a knowledge base, FAQs, or chatbots. This improves customer satisfaction by providing quick and easy solutions.
Capturing Richer Customer Analytics: CEPs make tracking and analyzing customer interactions easier, allowing businesses to identify patterns and trends. By digitizing every aspect of an experience, customer experience platforms can deliver data to a single truth source faster than a manual or semi-manual process. This customer feedback can improve products, services, and processes and proactively support customers.
How does a customer experience platform take pressure off call centers and agent teams?
Customer experience platforms often create self-service options that customers leverage to find answers to their questions without contacting the call center. This brings down the volume of calls and inquiries. Such a platform can also automate routine tasks such as ticket routing, categorization, and prioritization. This reduces the workload for call center agents and frees them up to focus on more complex issues that require human intervention.
CEPs can also deliver personalized interactions for customers. For example, these experiences can recommend products or services based on the customer's existing product set.
By reducing the volume of calls and inquiries and automating routine tasks, these versatile tech platforms take pressure off the call center and enable call center agents to focus on more complex and value-added tasks. This can improve the efficiency and effectiveness of the call center and ultimately lead to a better customer service experience.
What are the most critical metrics for evaluating CX automation experiences created with a CEP?
The most important metrics for CX automation experiences may vary depending on your business goals and industry. However, here are some key metrics that you should consider:
Customer Satisfaction (CSAT): This metric measures customers' satisfaction with their overall experience. It is typically measured using surveys or feedback forms that ask customers to rate their experience on a scale of 1 to 5 or 1 to 10.
Net Promoter Score (NPS): Many companies track NPS, and understanding the impact of experiences created with a platform on the score is often valuable.
Abandonment Rate: This metric measures the percentage of customers who abandon their call or interaction with Visual IVR before completing their task. A high abandonment rate may indicate that the Visual IVR is difficult to use.
First Call Resolution Rate: This percentage-based metric measures how many customer inquiries or requests are resolved on the first contact. It is typically measured as a percentage and is a key factor in customer satisfaction and loyalty.
Self-Service Usage Rate (for Self-Service Apps): This percentage metric measures the percentage of customers who use an experience to complete their tasks without needing assistance from a call center agent. A high self-service usage rate indicates that customers find the Visual IVR easy to use and that it effectively handles their needs.
Call Deflection Rate (for Visual IVR Apps): This metric measures the percentage of calls deflected from the call center by an experience. It is a percentage measure. A high call deflection rate indicates that Visual IVR provides customers with the necessary information.
Average Handle Time (for Apps Used in Agent-Led Calls): Average handle time assesses the average length of customer calls in which the experience is used. It helps to show how the experience adds to the efficiency of a call center team and lowers total call center costs.
First Call Resolution Rate (for Apps Used in Agent-Led Calls): This metric measures how many customer inquiries or requests are resolved on the first contact. It is typically measured as a percentage and is a key factor in determining customer satisfaction and loyalty.
How can I learn more about Callvu and CX automation?
Our team would be pleased to share a demo of our Callvu Customer Experience Platform. Just fill out this form or visit the Callvu homepage. We'll also tell you how to turn your support engagements into success stories that exceed customer expectations as part of a comprehensive customer relationship management strategy.